Zero-Knowledge Proofs: Trust Without Verification

For the last twenty years, the internet economy has operated on a toxic and fundamentally flawed premise: To prove something is true, you must hand over the underlying data.
If you want to buy a house, you must give the bank financial history, social security number, and tax returns to prove your financial capacity. If you want to access an age-restricted website, you must provide your birthdate. We trade privacy for verification.
This model treats data as an asset. But as the Chief Wise Officer knows, in an era of relentless cyberattacks and crippling regulatory fines (GDPR, CCPA), Data is not the new oil. Data is nuclear waste. It is expensive to store, highly volatile, and catastrophic if it leaks.
What if you could verify the truth of a statement without ever touching the toxic waste? What if a customer could prove to you that they are over 18, or that their bank account has sufficient funds, without ever revealing their birthdate or their actual balance?
This sounds like magic, but it is a cryptographic reality. It is called a Zero-Knowledge Proof (ZKP), and it is about to rewrite the rules of corporate risk, identity, and compliance.
The "Where’s Waldo" Analogy
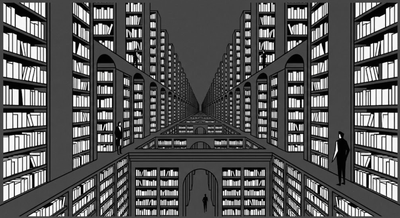
To understand how a ZKP works without getting buried in polynomial math, consider the game Where’s Waldo? (or Wally).
Imagine you and a friend are looking at a massive, incredibly complex Where's Waldo? poster. You find Waldo. Your friend doesn't believe you. You want to prove to your friend that you know exactly where Waldo is, but you do not want to show them the location, because that would ruin the game for them.
How do you prove you know the secret without revealing the secret?
You take a giant piece of opaque black cardboard, much larger than the poster itself. You cut a tiny Waldo-sized hole in the center of the cardboard. You then place the cardboard over the poster, moving it until Waldo's face appears perfectly through the tiny hole. Your friend looks at the hole. They see Waldo. They are 100% convinced that you know where he is. But because the cardboard covers the rest of the poster, they have zero knowledge of his coordinates on the page.
You have provided a Zero-Knowledge Proof. You proved the validity of a statement ("I know where Waldo is") while revealing zero knowledge about the underlying data (the coordinates).
The Strategic Shift: Cryptographic Truth
In the digital world, ZKPs (specifically protocols like zk-SNARKs and zk-STARKs) use complex cryptography to achieve this exact outcome. For a decade, this technology was mostly confined to privacy-focused cryptocurrencies (like Zcash) and blockchain scaling solutions (Ethereum rollups). But its true destiny is enterprise strategy.
The traditional corporate security model is "Trust, but Verify" (which practically means "Take the data, store it securely, and check it"). The ZKP model is "Verify without Trust." Here is how ZKPs alter the strategic landscape:
1. The End of the "Honeypot" Currently, companies hoard customer data to verify identities and transactions. This creates a massive "honeypot" for hackers. If Equifax didn't need to hold 147 million social security numbers to run their credit models, the infamous 2017 breach would have been mathematically impossible. With ZKPs, a company can query a user's cryptographic wallet: "Is this person's credit score > 700? True or False." The protocol returns a mathematical proof of "True." The company stores the proof, not the SSN. If the company is hacked, the hackers steal nothing but meaningless algebraic proofs. You cannot steal what isn't there.
2. Frictionless Compliance Regulators demand KYC (Know Your Customer) and AML (Anti-Money Laundering) checks. Historically, this meant forcing users to upload photos of their passports, a massive point of friction that destroys conversion rates. With ZKP-enabled digital IDs, a user can instantly submit a proof of citizenship and age without uploading a single document to your server. Compliance becomes instant, frictionless, and totally private.
3. B2B Collaboration Without Data Sharing Imagine two competing pharmaceutical companies who want to know if they are researching the same chemical compound, but neither wants to reveal their proprietary formula. Using ZKPs, they can mathematically compare their datasets and receive a simple "Yes/No" on whether there is an overlap, without ever exposing the actual formulas to each other. It enables collaboration in zero-trust environments.
The Philosophical Angle: The Burden of Knowledge
There is a profound philosophical lesson in Zero-Knowledge Proofs. We have been conditioned to believe that Knowledge is Power. We assume that the more granular data we possess about our customers, our supply chain, and our partners, the more control we have.
ZKPs introduce a Skeptical counter-narrative: Knowledge is a Liability. Just as Sextus Empiricus argued that holding rigid dogmatic beliefs causes mental anxiety, holding unnecessary data causes organizational anxiety.
The Chief Wise Officer understands that you do not need to "know" everything to operate effectively. You only need to know what is relevant to the transaction at hand. Everything else is just noise and risk.
Conclusion: De-risking the Future
We are entering the era of the Trustless Enterprise. This does not mean we stop trusting our customers; it means we remove the need for trust entirely by relying on mathematics.
When your compliance team asks for a larger budget to secure the massive database of user passports, the CWO should ask a different question: "Why are we holding the passports at all? How can we redesign this workflow to verify the truth without touching the data?"
Zero-Knowledge Proofs allow us to decouple verification from data ownership. The companies that embrace this will not just save millions in cybersecurity and compliance costs; they will offer a level of privacy that becomes a lethal competitive moat. Stop hoarding the toxic waste. Start trading in proofs.
No spam, no sharing to third party. Only you and me.




Member discussion